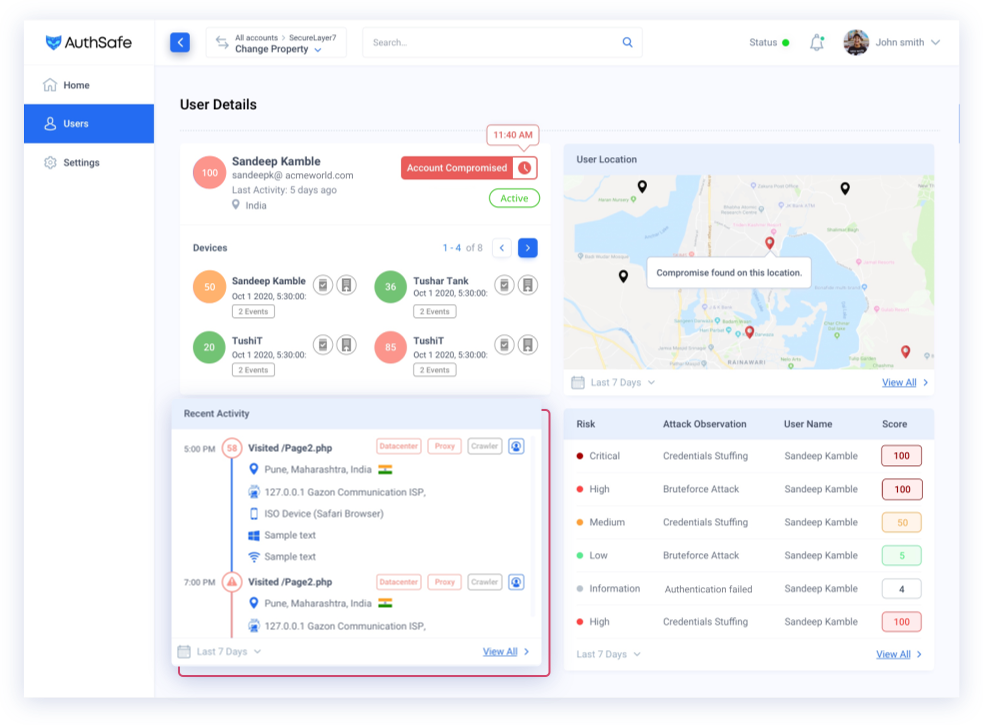
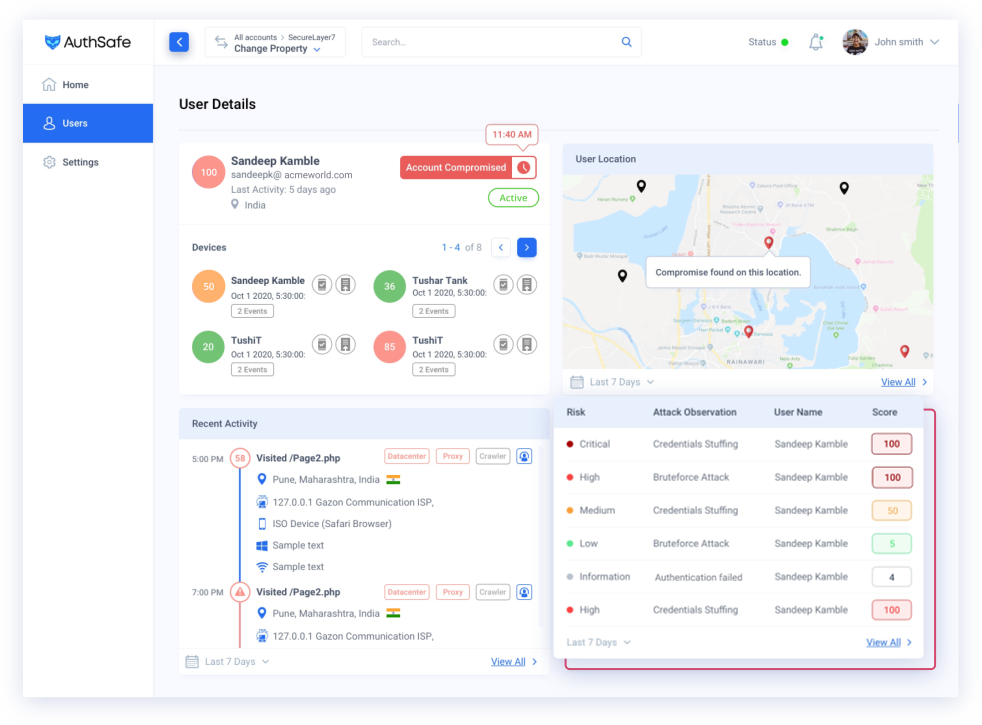
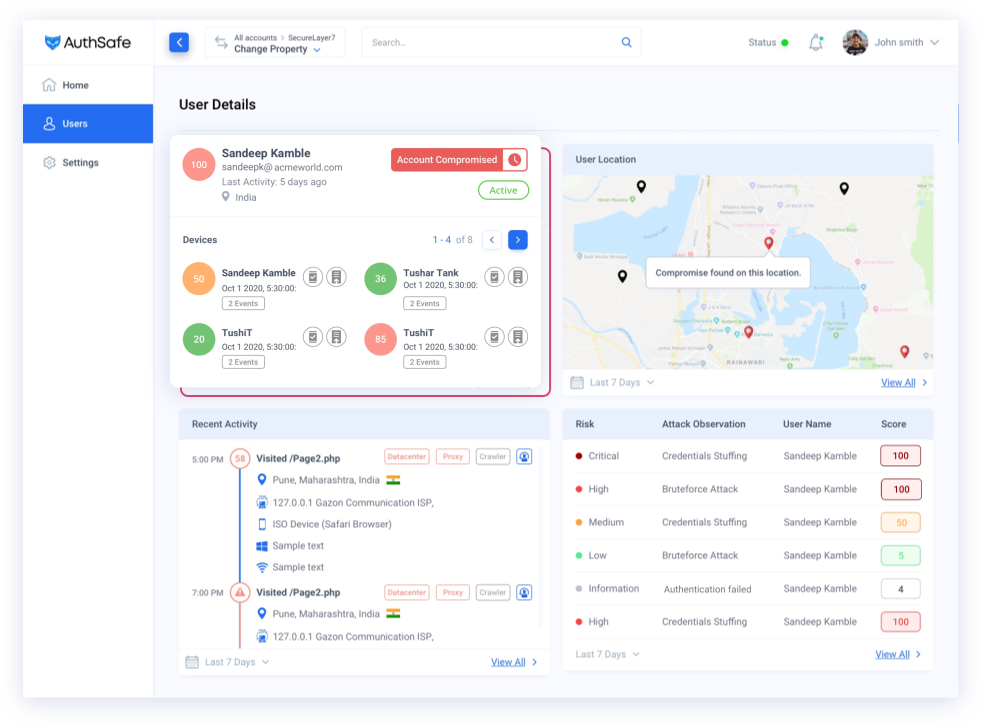
Everything Starts with Trust.
Authsafe Fraud Detection is trusted by every customer to keep their information safe. We have a team of experts who are continuously working to improve our detection capabilities, and we strive to provide the best possible service to our customers.